Managed Detection & Response (MDR)
Continuous testing finds new vulnerabilities early so you can fix issues before attackers exploit them.




Trusted by clients worldwide
Led by humans – enhanced by AI
Our MDR is the trusted extension of your security team

Human led. AI enhanced. Tech Agnostic.
MDR that builds resilience, expands meaningful visibility, and adapts to your tech stack without forcing change.
24/7 SOC
MDR led by humans, powered by AI so you never have to worry about resources.
Cyber Resilience
We help you increase cyber resilience with MDR that supports NIS2, DORA, and GDPR obligations.
Visibility
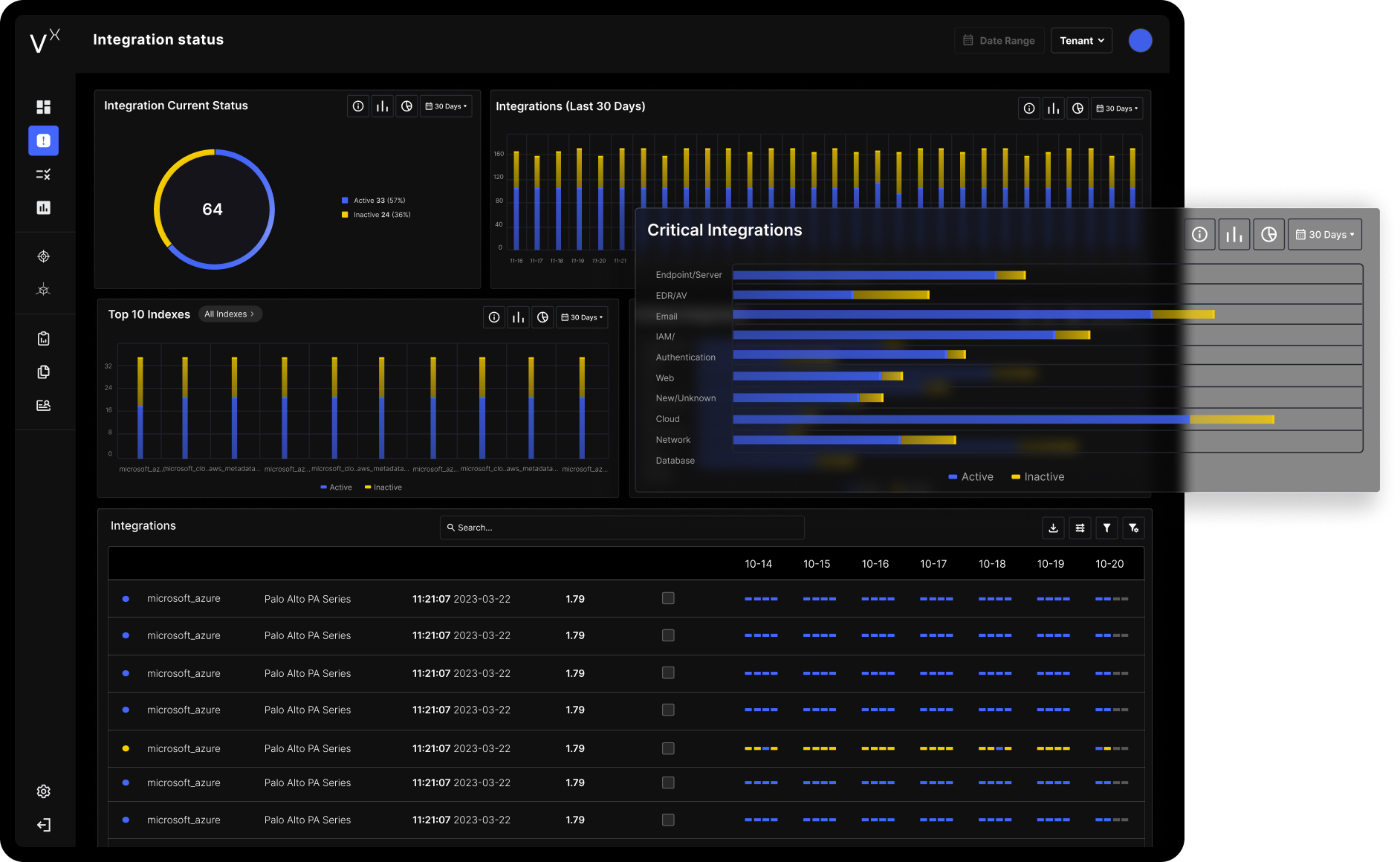
We are tech agnostic, helping you ingest telemetry from all sources, giving you a single source of truth for your security data.
Partnership
We are customer obsessed delivering security outcomes with transparency, a personal touch, and a partnership that always has your back.

.png)
.png)
.png)


Increase In Security Visibility
Faster Incident Response
Reduction in False Positives
Yearly FTE costs savings

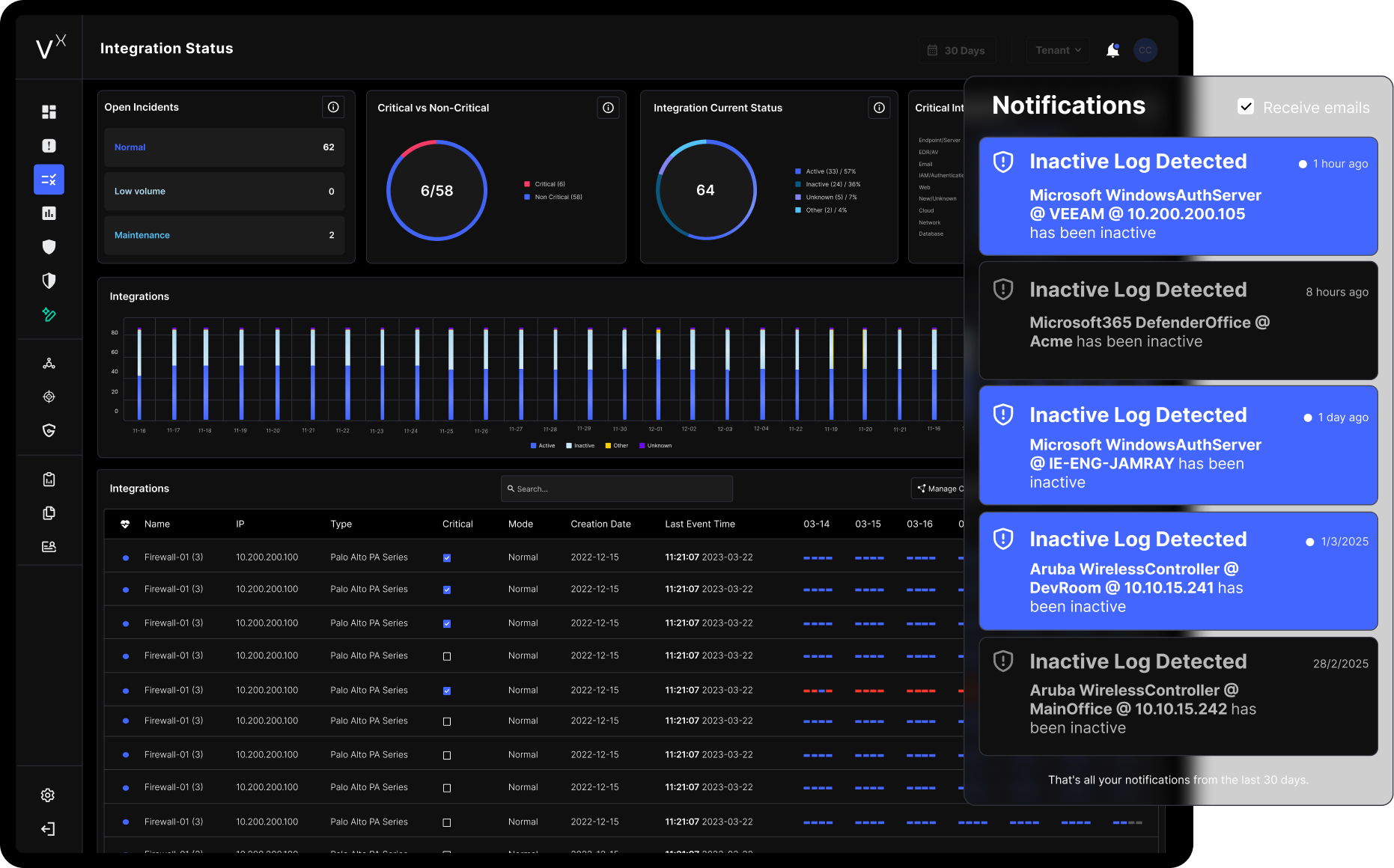
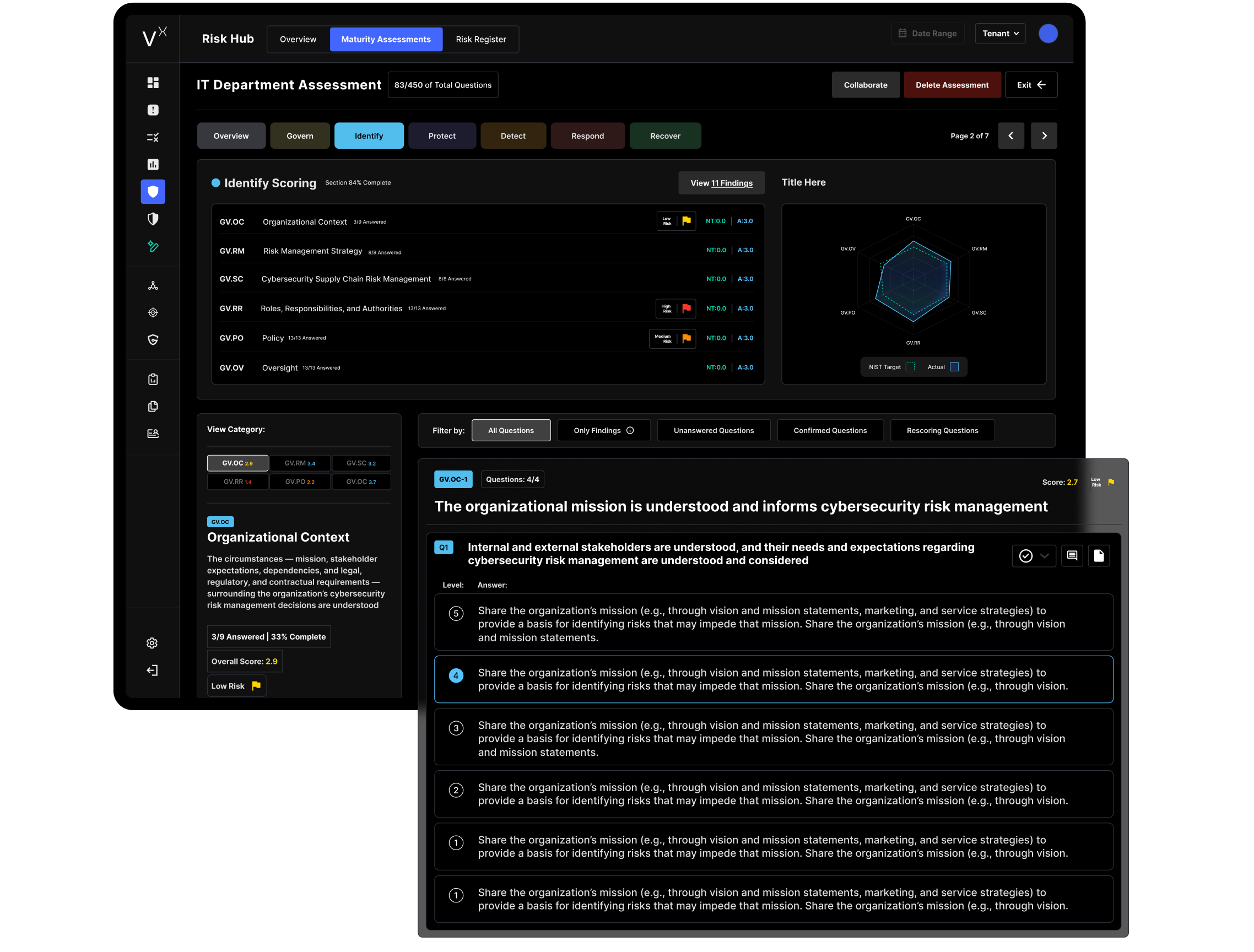
Explore the VisionX Command Center


Group IT Director
Dairygold

Information Security Manager
Clunetech

CTO
FBD Insurance

Director of IT & Technology Transformation
Royal College of Surgeons in Ireland
Led by human expertise and powered by the VisionX platform, we provide you with a 24/7 unbeatable Managed Detection & Response capability giving you transparent and consolidated security solutions.




