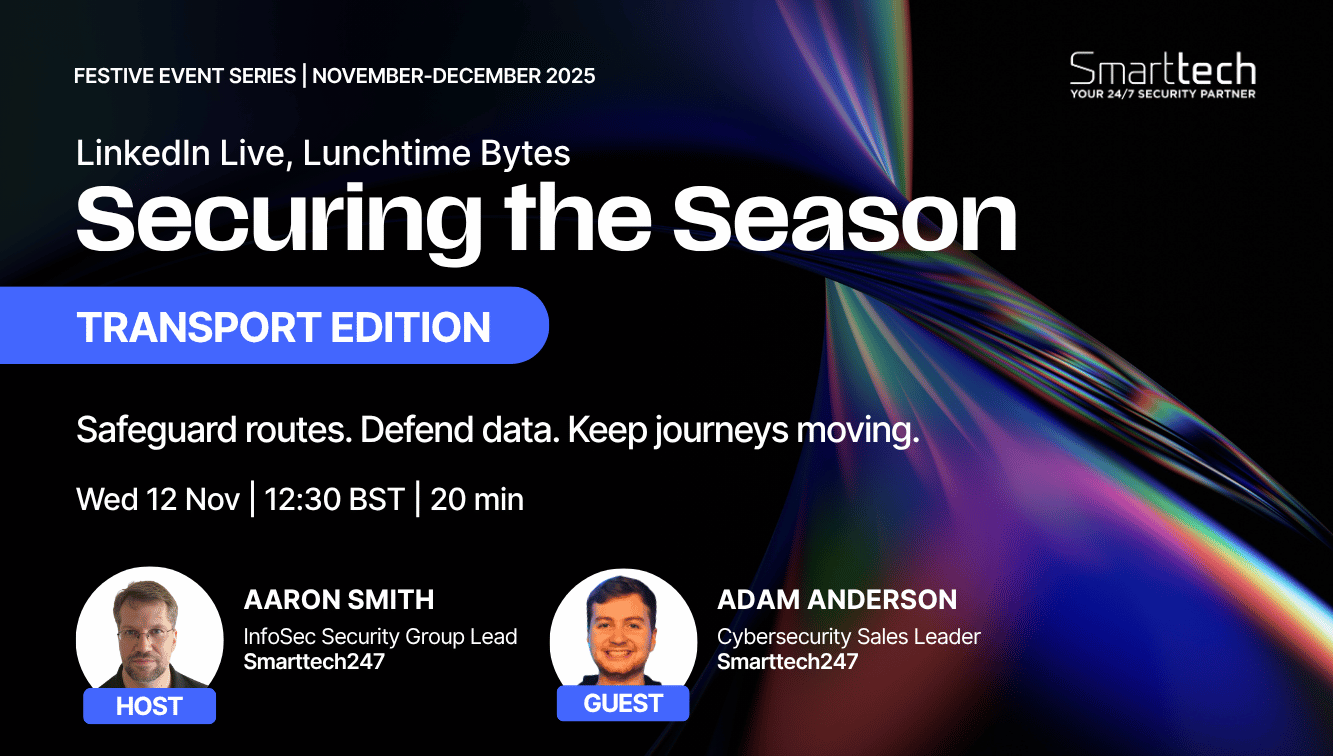
Seasonal Cybersecurity Risks for Technology Webinar
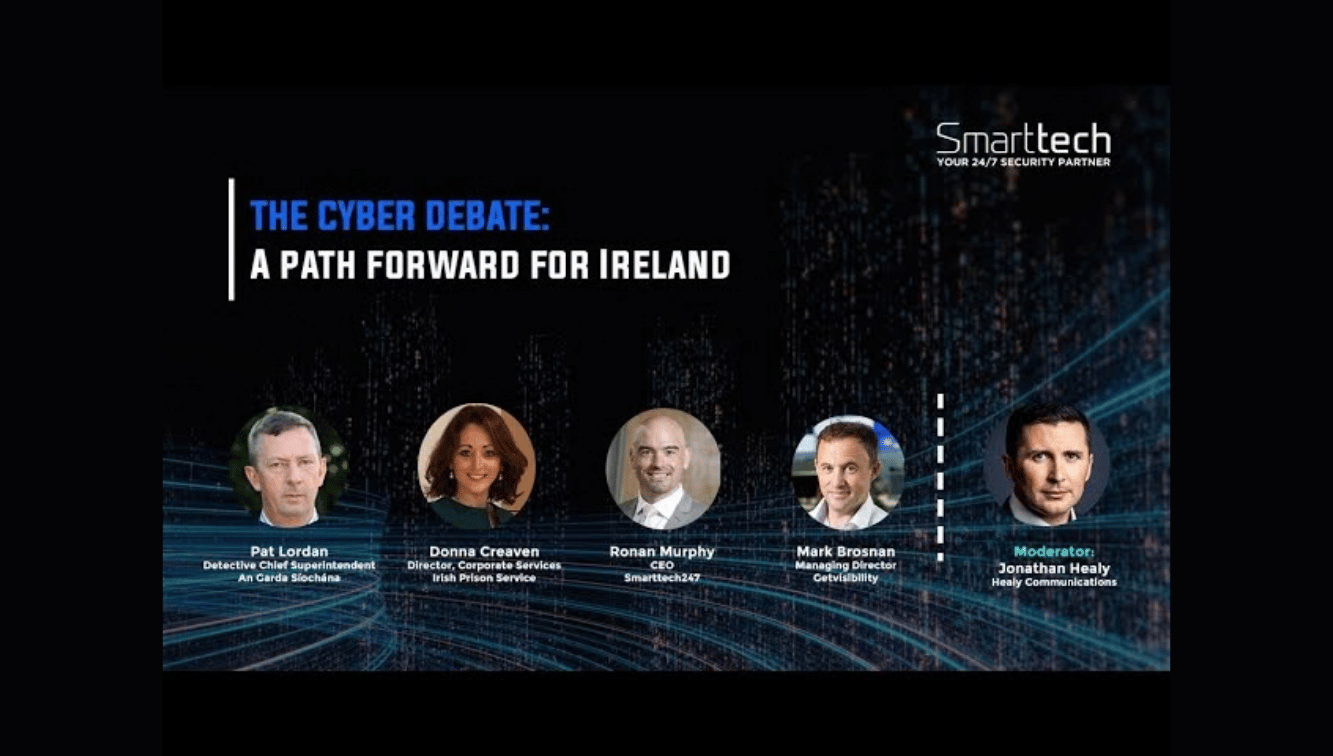
External Speakers
Key Strategic Takeaways
Cybersecurity is no longer a backend concern, it directly impacts revenue, customer trust, and the ability to close enterprise deals. With AI accelerating both attack scale and complexity, and investors scrutinising security maturity, weak controls now signal operational risk. Embedding security early reduces long-term cost, prevents disruption, and removes friction from sales, partnerships, and fundraising.
SMEs are disproportionately targeted because they combine valuable data with lower security maturity, making them efficient and profitable targets for attackers. Ransomware actors, in particular, adapt demands to match a company’s size, ensuring a higher likelihood of payment. For growing tech firms, aligning security maturity with business scale is critical to avoid becoming predictable “low-effort” targets.
A significant proportion of breaches now originate through third parties, meaning even well-secured companies can be exposed via their suppliers. As a result, security is no longer evaluated post-sale, it is a core requirement during procurement and due diligence.Technology vendors must proactively demonstrate security maturity or risk losing deals, damaging reputation, and exposing customer data indirectly.
Frameworks like NIS2, DORA, ISO 27001, and SOC 2 are no longer optional checkboxes, they are increasingly embedded in sales cycles and customer expectations. Late-stage compliance gaps can delay or completely derail deals, especially with enterprise buyers.Aligning with recognised standards early ensures smoother sales cycles, faster procurement, and stronger positioning in competitive markets.
Rapid growth often leads to excessive access, weak processes, and increased insider risk, whether through error or malicious intent. Without strong identity controls and monitoring, sensitive data and code can be exposed internally before any external attack occurs.Implementing MFA, least privilege, and continuous monitoring from day one provides high-impact protection and establishes a scalable security foundation.
- 00:00 Introduction to cybersecurity in the technology sector
- 01:32 Why cyber risk is accelerating across tech companies
- 02:10 Why security must be embedded from day one in startups
- 03:40 AI-driven threats and why smaller companies are being targeted
- 06:45 Regulation, compliance, and supply chain pressure on tech firms
- 08:00 How security requirements can delay or kill enterprise deals
- 10:27 Real-world supply chain breaches and third-party risk exposure
- 12:05 Insider threats, human error, and scaling risks in tech teams
- 14:48 Key regulations like NIS2 and DORA shaping the sector
- 16:53 Investor pressure and why security maturity impacts growth
- 19:23 Top cybersecurity priorities for scaling tech companies
- 20:49 Final takeaways on identity, monitoring, and control effectiveness

Protecting Critical Infrastructure | Palo Alto & Smarttech247 on Cyber Resilience
Ready to scale your security and compliance operations?
We protect your on-premise/cloud/OT environments - 24x7x365






.jpeg)



.png)