Seasonal Cybersecurity Risks for Transport Webinar
In-House Specialists
External Speakers
Key Strategic Takeaways
Transport environments are heavily dependent on OT systems designed for uptime and safety, not modern cyber resilience, making traditional security approaches difficult to apply. Legacy infrastructure and operational constraints mean patching, monitoring, and change management are inherently limited. Effective security starts with accepting this constraint and designing controls that work around uptime requirements rather than against them.
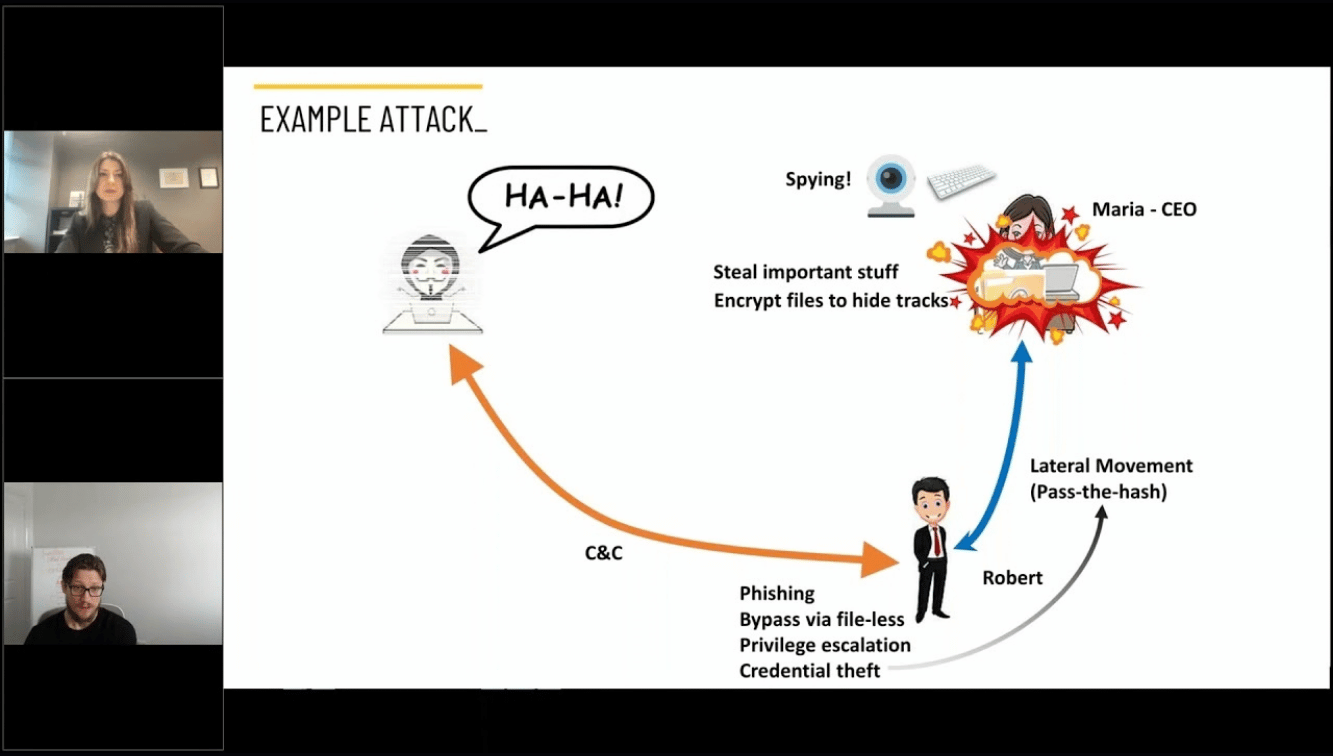
The core challenge is gaining control without introducing disruption, which makes visibility, segmentation, and safe testing essential. Many organisations still lack a complete view of assets, while flat networks increase the risk of lateral movement between IT and OT environments. A structured approach using continuous asset discovery, network segmentation, and digital twin environments allows teams to test and implement changes without risking live operations.
Digital twins are increasingly used to model operational systems and test scenarios, including cyberattack simulations, improving preparedness and decision-making. However, they also introduce new attack surfaces, particularly when connected to live operational data. To be effective and safe, digital twins must be treated as production assets, with proper access controls, monitoring, and governance to prevent them becoming intelligence sources for attackers.
Attackers are evolving from opportunistic ransomware toward multi-stage campaigns designed to disrupt operations, often entering through less secure peripheral systems like ticketing, Wi-Fi, or third-party platforms. Supply-chain compromise is a particularly effective vector, enabling widespread impact from a single point of entry. Defence strategies must prioritise early detection, lateral movement prevention, and protection of interconnected systems rather than focusing solely on perimeter security.
In transport, the critical factor is not whether an incident occurs, but how quickly it is detected, contained, and recovered from, given the immediate operational and public impact of disruption. Organisations that perform best have integrated IT/OT visibility, automated containment actions, and rehearsed response plans. Building resilience means reducing response time through automation, enforcing strict third-party controls, and preparing for future risks from technologies like AI and quantum computing.
- 00:00 Introduction to transport cybersecurity and OT-heavy environments
- 01:06 Why securing OT systems without downtime is so difficult
- 02:16 Core strategies: visibility, segmentation, and simulation
- 03:05 Digital twins and testing security without disrupting operations
- 04:22 Evolving threats: ransomware, disruption, and multi-stage attacks
- 05:41 Supply chain attacks and vendor-driven entry points
- 06:08 Connected systems, IoT, and expanding attack surface
- 07:55 Why resilience depends on detection, response, and recovery speed
- 08:57 Breaking silos between IT and OT for better security outcomes
- 10:01 Real-world impact: cyber incidents affecting national operations
- 11:25 Managing third-party risk and enforcing supplier controls
- 14:29 Future risks: AI, quantum computing, and emerging technologies

Protecting Critical Infrastructure | Palo Alto & Smarttech247 on Cyber Resilience
Ready to scale your security and compliance operations?
We protect your on-premise/cloud/OT environments - 24x7x365






.jpeg)