External Speakers

Pavel Mucha

Key Strategic Takeaways
Ransomware is no longer a single event but a sequence of actions including phishing, command-and-control, privilege escalation, and lateral movement before impact. Attackers aim to remain undetected long enough to reach high-value systems and data. Understanding the full attack chain allows organisations to identify multiple points where detection and containment can break the sequence early.
Attackers increasingly use built-in system tools like PowerShell, Regsvr32, and Bitsadmin to execute attacks without triggering traditional signature-based controls. This “living-off-the-land” approach blends malicious activity with normal operations. Defence requires behavioural analysis and context-aware detection rather than reliance on known malware signatures.
Traditional alerting produces fragmented signals that require manual investigation, slowing response. Modern approaches group related activity into a single, contextualised incident view, enabling faster understanding of root cause and impact. This shift from event-based alerts to attack narratives improves analyst efficiency and accelerates containment decisions.
Effective response capabilities allow teams to isolate endpoints, terminate malicious processes, and contain threats without breaking critical systems. Guided response mechanisms help avoid operational damage while stopping attacker progression. Speed, clarity, and controlled action are key to limiting impact during active incidents.
Attack simulations reveal weaknesses in detection, response coordination, and operational readiness that are often invisible in day-to-day operations. They test not just tools, but decision-making, communication, and execution under pressure. Organisations that regularly simulate attacks are better prepared to respond decisively when real incidents occur.
- 00:00 Intro + context (recent major cyber incidents)
- 03:05 Cybereason overview (endpoint + AI positioning)
- 06:06 Attack scenario setup (attacker / victim / defender)
- 07:13 Phishing entry point (macro-enabled Excel)
- 17:19 Initial compromise (DGA + fileless execution)
- 20:40 Detection model explanation (MalOps vs alerts)
- 33:50 Response actions (kill process, isolate, guided response)
- 36:17 Attack escalation (privilege escalation + persistence)
- 41:52 Lateral movement (pass-the-hash to CEO machine)
- 44:55 Ransomware deployment (PowerShell-based)
- 46:12 Detection across attack chain
- 50:28 Attack tree + full visibility walkthrough
- 52:53 Threat hunting (query-based detection)
- 56:30 Platform summary + Q&A
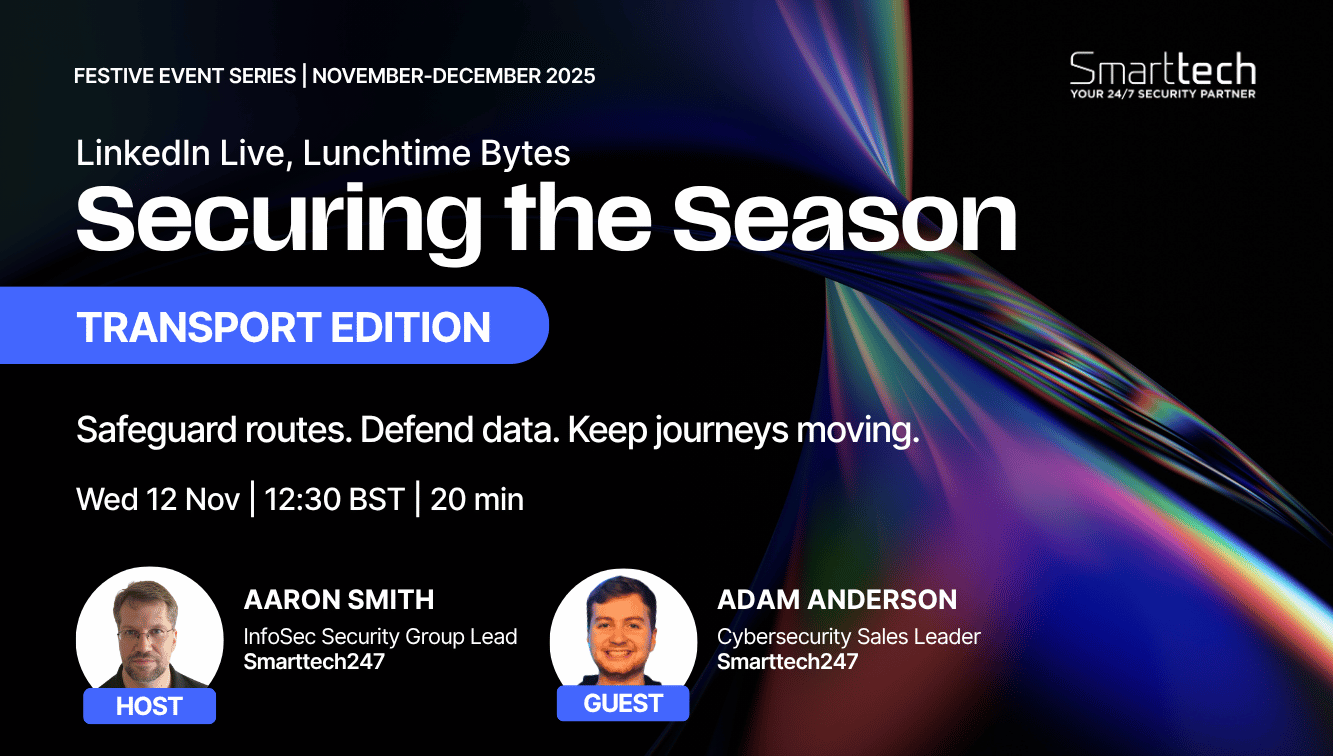
Seasonal Cybersecurity Risks for Transport Webinar
Ready to scale your security and compliance operations?
We protect your on-premise/cloud/OT environments - 24x7x365






.jpeg)



.png)