Seasonal Cybersecurity Risks for Manufacturing Webinar
External Speakers
Key Strategic Takeaways
Attackers target manufacturers because disruption translates directly into financial pressure, forcing faster ransom payments due to production downtime, supply delays, and contractual penalties. Beyond ransomware, intellectual property has become a high-value target, often easier to monetise and harder to detect than financial data. Manufacturers must treat cybersecurity as an operational risk, where protecting uptime and IP is directly tied to revenue and competitive advantage.
Unlike financial data theft, IP loss often goes undetected for years, only surfacing when competitors release similar products or market share declines. This delayed visibility makes it one of the most damaging forms of cyberattack, eroding innovation and long-term profitability. Defence requires stronger monitoring of data movement, tighter access controls, and a clear understanding of where critical intellectual property resides.
Manufacturing environments rely on legacy OT systems that prioritise reliability over security, with limited patching options and minimal built-in protections. As IT and OT converge, these historically isolated systems are now exposed to broader enterprise and external threats. Security strategies must adapt by introducing segmentation, visibility, and controls that respect operational constraints rather than attempting traditional IT-first approaches.
Highly interconnected supply chains introduce risk through vendors, contractors, and partners with varying levels of security maturity. Attackers increasingly exploit these weaker links to gain indirect access to larger, better-defended manufacturers. Organisations need continuous visibility into third-party access, enforce least-privilege controls, and implement contractual and technical safeguards to reduce supply-chain risk.
Many manufacturing organisations, especially smaller firms, lack the resources for advanced security programmes but can significantly reduce risk through foundational controls. Identity security, network segmentation, immutable backups, and continuous monitoring provide the highest impact in limiting both attack success and recovery time. The focus should be on knowing critical assets, testing recovery regularly, and building a security baseline that supports fast containment and operational continuity.
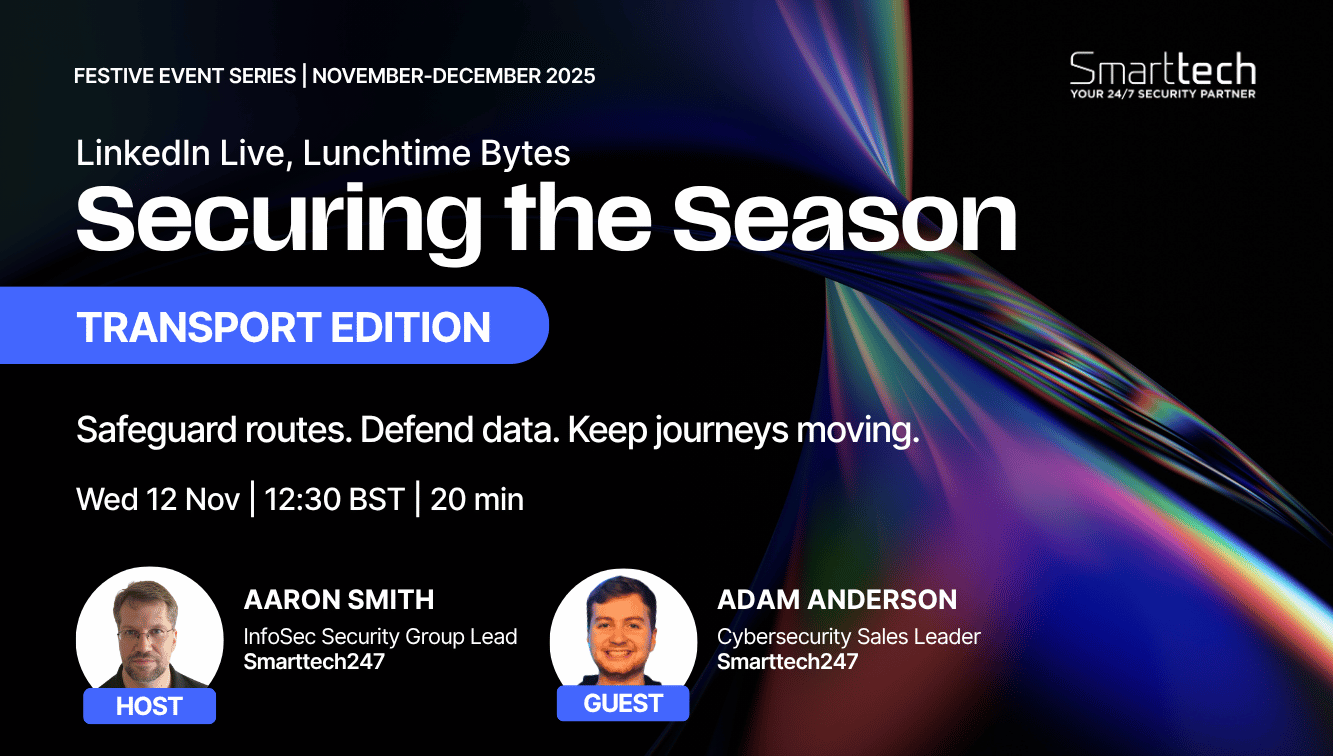
- 00:00 Introduction to Securing the Season and why manufacturing comes first
- 01:17 Why manufacturers have become prime targets for cyber attacks
- 02:12 How IP theft can damage revenue, reputation, and long-term competitiveness
- 05:25 Why OT environments and legacy systems are so hard to secure
- 06:27 Supply chain complexity and the hidden risk of connected partners
- 07:47 Why ransomware and ERP attacks spike during the holiday period
- 10:36 Who is behind manufacturing cyber attacks and what motivates them
- 13:05 How ransomware groups operate like highly efficient criminal businesses
- 15:19 The most common attacks hitting manufacturers right now
- 18:14 Why identity, AI, and digital transformation are reshaping manufacturing risk
- 20:16 The most important security controls manufacturers should prioritise
- 23:04 Practical cybersecurity priorities for smaller manufacturing companies

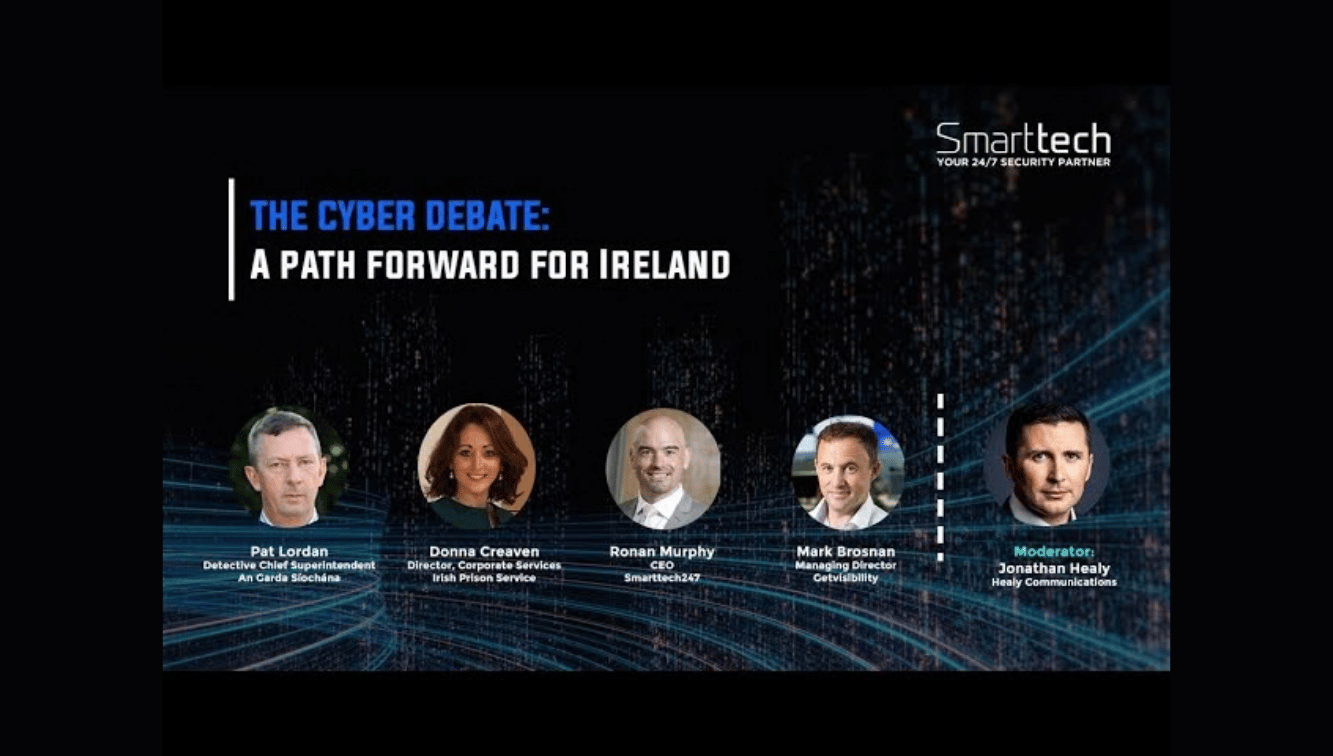
Protecting Critical Infrastructure | Palo Alto & Smarttech247 on Cyber Resilience
Ready to scale your security and compliance operations?
We protect your on-premise/cloud/OT environments - 24x7x365






.jpeg)



.png)