Detecting and Mitigating Insider Threats Webinar
External Speakers

Richard Pace


Jan Tietze


Mark Brosnan

Key Strategic Takeaways
The majority of insider incidents come from everyday behaviour, phishing clicks, misuse of access, or poor decisions under pressure, not espionage or deliberate sabotage. Organisations that over-focus on rare “malicious insiders” miss the far more common accidental risks. Effective programmes prioritise reducing human error and misuse at scale rather than chasing edge-case threats.
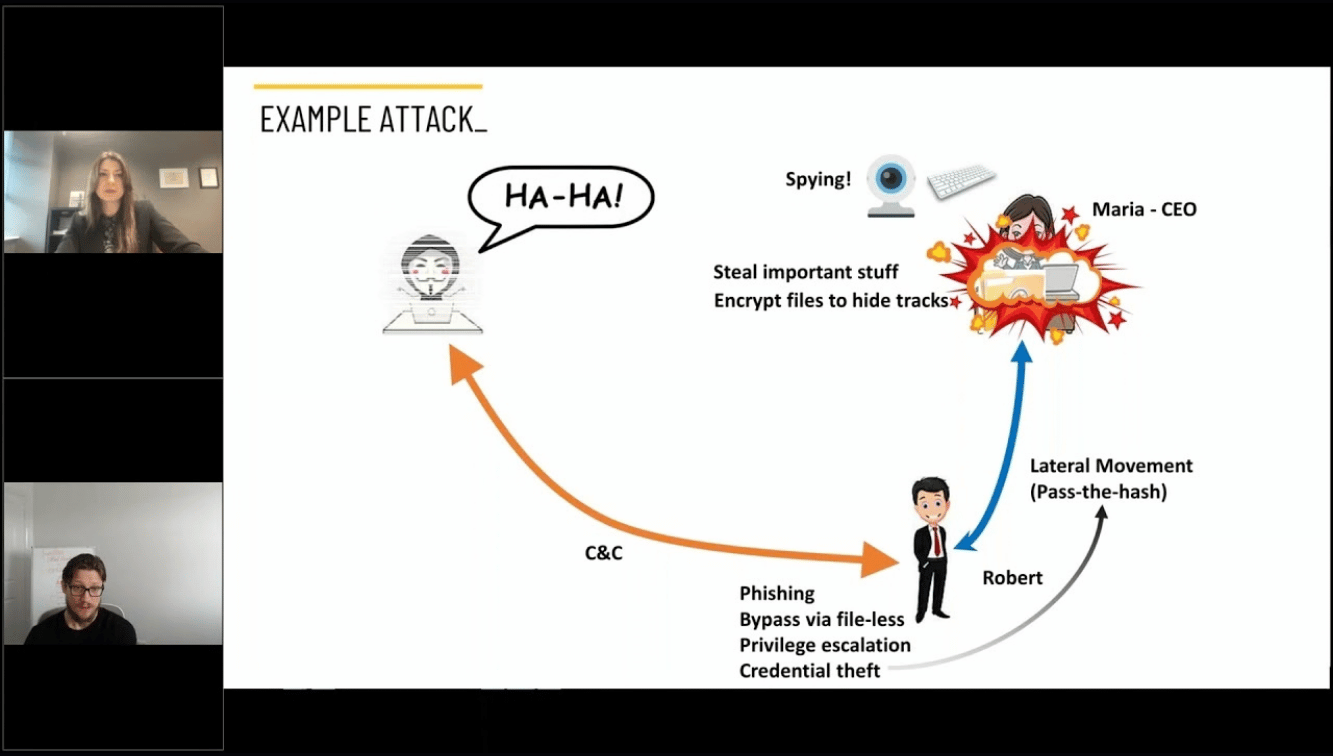
Third-party software, vendors, and integrations effectively introduce external actors with insider-like access. High-profile incidents show that trusted systems can become attack vectors, often with excessive permissions and limited visibility. Prevention is not enough; organisations must focus on detecting abnormal behaviour and attacker objectives across trusted environments.
Most organisations are overwhelmed because they try to protect everything equally. A data-first approach focuses on identifying the most sensitive and valuable data and applying stronger controls where impact is highest. Without understanding data sensitivity at scale, controls become noisy, disruptive, and ultimately ignored.
Traditional DLP struggles with complex, unstructured data and generates excessive false positives. Modern AI-driven classification can identify sensitive content more accurately and provide real-time guidance within user workflows. This reduces accidental data exposure while reinforcing user awareness without relying solely on formal training.
Insider risk programmes fail when policies are unclear, expectations are not reinforced, and employees do not understand what is allowed. At the same time, security teams must rely on behavioural detection and automated response to scale beyond manual monitoring. Clear governance, combined with real-time detection and rapid response, is what limits damage when insider activity occurs.
- 00:08 Introduction: Insider threat landscape and key speakers
- 01:18 Insider threat types: malicious vs unintentional (UIT)
- 02:29 Real-world cases: Waymo IP theft and Boeing espionage
- 04:13 Insider threat reality: accidental users vs sophisticated attacks
- 05:31 Supply chain attacks as “imported insiders” (SolarWinds, MOVEit)
- 06:29 Limits of detecting state-sponsored insiders
- 10:00 Data-centric security and risk-based prioritisation (CMMC context)
- 13:30 AI solving data classification at scale (vs legacy DLP)
- 16:04 MOVEit and why prevention alone fails (shift to behaviour detection)
- 20:17 Behaviour-based detection vs traditional network monitoring
- 22:19 Human behaviour, culture, and policy gaps as root cause
- 30:22 Misalignment: GRC vs security vs business reality
- 37:01 Culture change through behavioural training and simulation
- 40:05 Building insider threat programmes without massive resources
- 46:34 AI risks: data leakage via LLMs and misuse
- 49:51 Protecting IP (e.g. code) with AI-driven classification
- 55:00 LLMs vs narrow AI models for security use cases
Seasonal Cybersecurity Risks for Transport Webinar
Ready to scale your security and compliance operations?
We protect your on-premise/cloud/OT environments - 24x7x365






.jpeg)