Social engineering has moved well beyond email. Vishing, deepfakes, and ClickFix-style prompts are convincing users to take unsafe actions in real time.

.svg)
When breach inevitability is the modern reality, what matters most is how fast and decisively an organisation responds. Detection identifies that something may be wrong. Incident response management executes response actions in real time. An effective cybersecurity incident response plan sits between the two, providing the documented framework that turns detection into controlled, defensible action. It defines decision authority, escalation paths, and coordination so response activities remain aligned with legal, regulatory, and business requirements.
The National Institute of Standards and Technology (NIST) defines best practice for incident response planning in its Computer Security Incident Handling Guide (SP 800-61). NIST emphasises that effective response depends on clear roles, structured coordination, and predefined communication, not just technical controls. Incident response plans should include defined responsibilities, escalation procedures, response metrics, and a process for continuous improvement based on lessons learned from real incidents.
For many organisations, incident response and MDR services provide the operational capability to activate these plans in practice, delivering continuous monitoring, specialist expertise, and rapid response support when incidents occur.
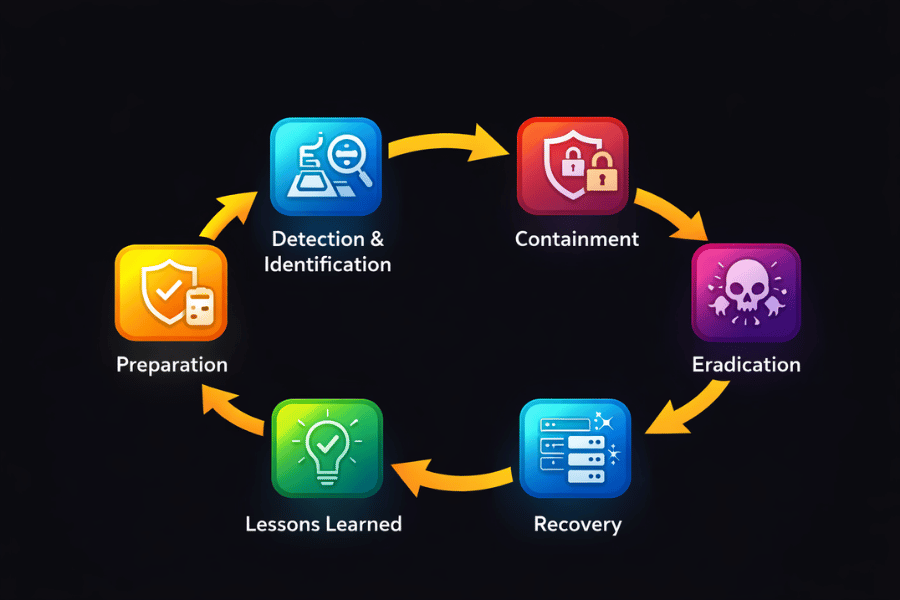
1. Preparation
Preparation establishes the authority, structure, and readiness that govern how an organisation responds to a cybersecurity incident. It defines decision ownership, escalation paths, and accountability so actions can be taken quickly and consistently.
An effective incident response plan should establish:
- clear roles across technical teams, legal, compliance, communications, and executive leadership
- defined reporting channels so staff can recognise and escalate suspicious activity without hesitation
CISA guidance emphasises the importance of organisation-wide readiness, where incident awareness and reporting are supported by training and clear responsibility.
Legal and external coordination should be established in advance. The plan should:
- be reviewed with legal counsel
- define how external incident response providers, regulators, and law enforcement are engaged
- maintain key contacts, documentation, and escalation procedures in accessible formats, including during system outages or degraded conditions
Preparation should also include stakeholder and communication readiness. Internal and external stakeholders are identified in advance, with pre-approved communication frameworks to support consistent messaging. Regular reviews and tabletop exercises, as recommended by CISA, help ensure the incident response plan remains current and effective as the organisation and threat landscape evolve.
2. Detection & Analysis
Detection and analysis should define the point at which an organisation formally becomes aware of a security incident and activates its incident response plan. In a GDPR context, this moment is critical, as regulatory obligations begin once an organisation can reasonably determine that a security incident involving personal data has occurred.
The incident response plan should define how detection outcomes are assessed and escalated. Alerts generated through SIEM, EDR, or Managed Detection and Response (MDR) services providing 24/7 monitoring should be evaluated to determine:
- whether the activity constitutes a security incident
- whether personal data is involved
- whether the event qualifies as a reportable personal data breach
The plan should establish clear decision authority for declaring an incident, notifying legal and compliance teams, and triggering regulatory timelines. By formalising these decision points in advance, organisations should be able to demonstrate timely awareness and appropriate organisational measures, as expected under GDPR Articles 32 and 33.
3. Containment
Containment should be governed by the authority and coordination structures defined in the incident response plan. Once an incident is confirmed, designated leadership roles should be activated to prioritise actions, manage escalation, and maintain control.
The plan should specify approved containment measures, including:
- using micro-segmentation to limit lateral movement
- blocking suspicious IP addresses and traffic
- isolating affected systems to prevent further spread
It should prioritise short-term containment to stop active spread before moving to long-term containment, such as system rebuilds or architectural changes. The plan should also define how strategic trade-offs are made, including situations where maintaining limited attacker visibility may be appropriate to support investigation while containment activities continue.
Clear approval thresholds should ensure containment actions are decisive, consistent, and aligned with business, legal, and operational risk.
4. Eradication
Eradication should focus on fully removing the root cause of the incident and preventing recurrence, guided by the controls and approval paths defined in the incident response plan.
The plan should require eradication activities to include:
- removing malware and malicious tooling
- eliminating persistence mechanisms
- revoking compromised credentials
- patching exploited vulnerabilities
It should emphasise the importance of understanding the full attack vector to ensure no backdoors or residual access remain. Validation of eradication should be mandatory, using scan tools, forensic analysis, and threat hunting support where appropriate.
The plan should define who approves remediation actions, when external expertise may be engaged, and how findings are documented. This ensures eradication activities are thorough, auditable, and aligned with broader security and compliance objectives.
5. Recovery
Recovery should return systems to normal operation in a controlled, prioritised manner once containment and eradication are complete. NIST guidance highlights recovery as a phased process, designed to restore operations while reducing the risk of repeat compromise.
The incident response plan should define:
- who is authorised to approve systems returning to production
- how recovery actions are prioritised based on risk and business impact
Recovery activities should include:
- restoring systems from verified clean backups or rebuilding where required
- replacing compromised files and resetting credentials
- remediating vulnerabilities exploited during the incident
The plan should require heightened visibility during recovery, including:
- increased system logging
- enhanced monitoring to detect instability or reinfection
For higher-risk incidents, systems may be reintroduced gradually or in limited operating modes to validate behaviour before full operations resume.
All recovery actions should be documented, approved, and reviewed to ensure traceability and alignment with security, operational, and compliance requirements.
6. Post-Incident Review & Learning
Post-incident review should ensure that every incident strengthens future response capability. The incident response plan should require a structured “lessons learned” review after major incidents, and periodically after lower-severity incidents where resources allow. Reviews should take place within days of incident closure to ensure accuracy and accountability.
The plan should define required participants, including:
- technical response teams and management
- legal, compliance, and communications
- external partners involved in response or investigation
Each review should establish a shared understanding of:
- what happened and when
- how the incident was detected and escalated
- whether documented procedures were followed and were effective
- where delays, gaps, or decision friction occurred
The review should also examine:
- whether any response actions inhibited recovery
- what information would have been useful earlier
- how coordination and information sharing could be improved
- what corrective actions can prevent similar incidents
Outputs from the review should include:
- updated playbooks and escalation paths
- revised detection indicators and monitoring priorities
- identified tooling, visibility, or resource gaps
Findings should be documented and fed directly into training and tabletop exercises. This ensures lessons learned are operationalised, not archived, and that the incident response plan continues to evolve with the threat landscape.
What makes this strategy work
What makes an incident response plan for cybersecurity effective is continuous improvement. Each incident should strengthen the organisation’s ability to detect, decide, contain, and recover faster over time.
Effective programmes share a few core characteristics:
- Clear roles and authority so decisions are made quickly and consistently
- Structured escalation to reduce delay and confusion under pressure
- Context and intelligence to focus effort where it reduces impact
Measurement should be built into the plan to support improvement. Useful indicators include:
- time to detect and confirm incidents
- time to triage, contain, and recover
- effort required to resolve incidents
- business and data impact, including recurrence
Communication should follow predefined paths, keeping internal and external stakeholders informed at appropriate stages. After recovery, a structured lessons learned review should take place within days, involving all relevant teams. Reviews should examine what happened, how effectively response activities worked, and where changes are needed.
Findings should result in:
- updated policies and playbooks
- improved training and exercises
- better visibility and controls
Use this six-step model as a roadmap for a living incident response programme that evolves alongside threats, technology, and organisational change.
Read Our Latest Blogs

Attackers are increasingly exploiting trusted software workflows to trick technical users into executing malicious payloads.
.png)
Palo Alto firewall RCE, Canvas LMS data breach affecting 275 million users, and a nine-year Linux kernel privilege escalation bug.






.jpeg)





