Protecting Data in the Age of GenAI Part Two Webinar
External Speakers

Chris O' Donoghue
.png)

John McGuinness
.png)
Key Strategic Takeaways
Most organisations deployed DLP without understanding what data they had, where it lived, or who could access it, resulting in reactive policies and blind spots. DSPM changes this by continuously discovering, classifying, and monitoring sensitive data across environments. Effective data protection starts with visibility, without it, DLP is just enforcing rules on assumptions.
The traditional perimeter model no longer works, as data now moves across cloud platforms, devices, and geographies outside controlled network boundaries. Security controls must operate consistently across endpoints, SaaS, and web channels, regardless of where users are working. Modern data protection shifts from preventing “data leaving” to controlling how data is accessed, shared, and used throughout its lifecycle.
Running separate DLP policies across multiple tools leads to inconsistency, gaps in coverage, and limited visibility into data movement. Without a unified policy layer, organisations struggle to enforce controls consistently or produce reliable audit trails. A single policy framework applied across all control points is essential to reduce complexity and ensure effective, scalable protection.
Static DLP rules fail because they treat all users and behaviours the same, regardless of context. Risk-adaptive protection introduces dynamic enforcement based on user behaviour, activity patterns, and insider risk signals. This allows organisations to balance security with usability, tightening controls only when risk increases while enabling normal operations otherwise.
Regulations like NIS2 are making rapid incident reporting mandatory, which is impossible without clear visibility into what data was accessed or exposed. Organisations can no longer afford uncertainty during a breach. Mature DSPM and DLP capabilities enable faster, evidence-based responses, ensuring organisations can meet regulatory requirements and maintain trust under pressure.
- 00:00 Introduction to the next step after DSPM: protecting data with DLP
- 01:12 Why legacy DLP often failed without real data visibility
- 02:41 DSPM as the missing stage in a mature data security journey
- 03:53 Data loss prevention vs data life protection in cloud environments
- 06:37 Why data security must extend across endpoints, cloud, web, and email
- 09:44 Building one unified DLP policy across all control points
- 11:41 Risk-adaptive protection and changing controls based on user risk
- 13:18 The five building blocks of modern data security everywhere
- 15:43 What differentiates advanced DLP from basic market alternatives
- 19:31 Protecting cloud data, unmanaged apps, and regulatory obligations
- 22:09 What to look for when evaluating DLP vendors and capabilities
- 26:46 Where organizations should start with DSPM, DLP, and compliance needs

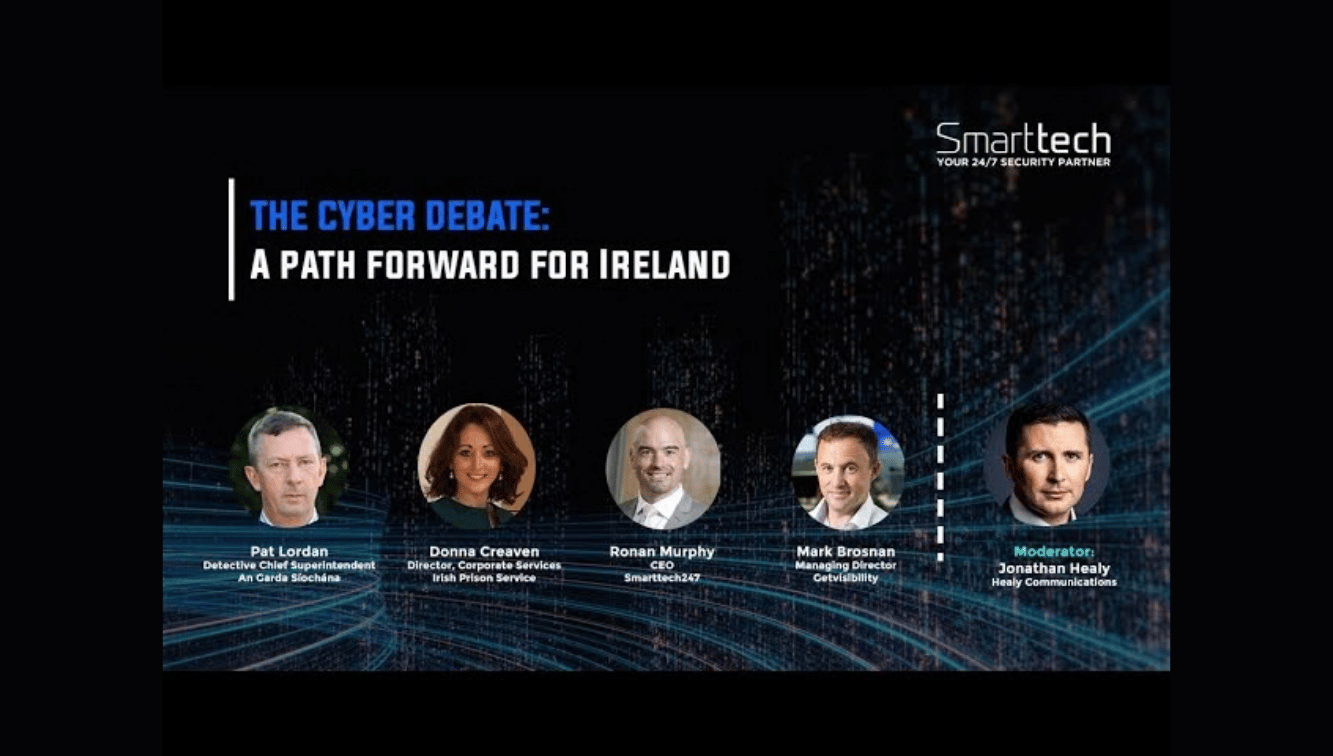
Protecting Critical Infrastructure | Palo Alto & Smarttech247 on Cyber Resilience
Ready to scale your security and compliance operations?
We protect your on-premise/cloud/OT environments - 24x7x365






.jpeg)