Protecting Data in the Age of GenAI Part One Webinar
External Speakers

Chris O' Donoghue
.png)

John McGuinness
.png)
Key Strategic Takeaways
Organisations rely on data for growth, analytics, and competitive advantage, but attackers target that same data for extortion and resale. As access to data expands across users, systems, and platforms, so does the attack surface, turning data exposure into a direct business risk. This dual role, asset and liability, has forced boards to treat data security as a core business priority rather than a technical issue.
Frameworks like GDPR, NIS2, and ISO 27001 have shifted accountability upward, requiring demonstrable controls, auditability, and rapid incident reporting. Boards can no longer delegate data security entirely to IT without risking regulatory penalties and reputational damage. Cybersecurity has become a governance issue, where leadership must prove oversight, not just assume it exists.
Many firms still cannot clearly identify what sensitive data they hold, where it resides, who has access, or how it is being used. Large volumes of “dark data” sit outside visibility, creating hidden exposure that attackers can exploit once inside the environment. Without answering these fundamental questions, other security investments lose effectiveness because organisations are protecting systems, not the data attackers actually want.
Dark data, shadow data, and redundant or obsolete information significantly increase attack surface while making it harder to prioritise protection. Data is constantly copied, shared, and stored outside controlled environments, often for convenience rather than necessity. Reducing unnecessary data and enforcing control over where it lives is as important as defending against external threats.
Data Security Posture Management provides the visibility, classification, and risk prioritisation needed to manage data at scale across cloud and on-prem environments. By continuously monitoring data movement and ownership, it enables organisations to assign accountability, automate remediation, and support downstream controls like DLP. This shifts data security from periodic audits to continuous governance, making it measurable, defensible, and aligned with business risk.
- 00:00 Introduction to DSPM and why data security is being rethought
- 01:15 Why data has become both a competitive asset and a hacker target
- 03:17 The five core questions every organization should answer about its data
- 05:33 Dark data, unknown data, and why most companies lack visibility
- 06:31 Data sprawl, shadow data, and the growing storage attack surface
- 08:33 What DSPM is and why visibility is the first step in protection
- 09:11 How DSPM discovers, classifies, and maps sensitive data flows
- 10:55 Risk assessment, overpermissioning, and automated remediation
- 12:43 Why DSPM is now a boardroom conversation
- 13:51 Cloud, zero trust, and why identity is the new perimeter
- 15:07 How AI is making data discovery and classification finally scalable
- 16:31 The business value of DSPM: compliance, remediation, and data hygiene

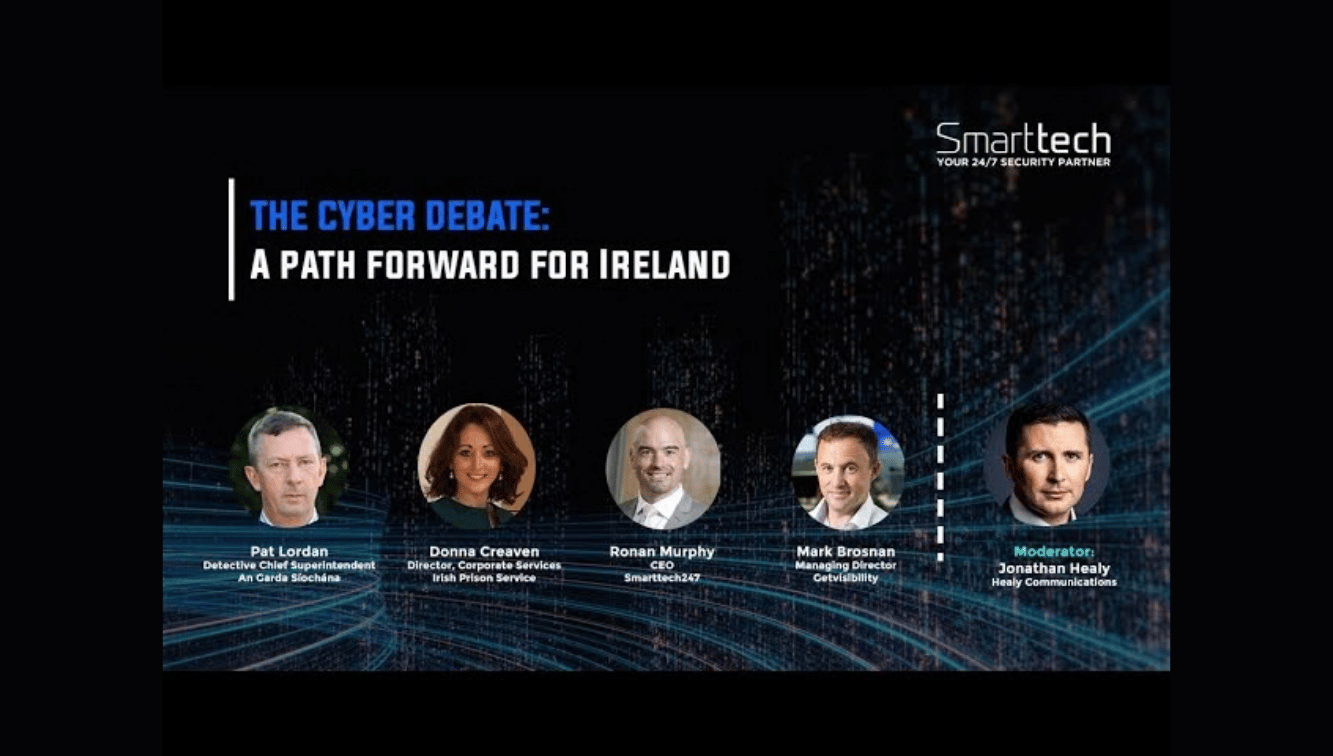
Protecting Critical Infrastructure | Palo Alto & Smarttech247 on Cyber Resilience
Ready to scale your security and compliance operations?
We protect your on-premise/cloud/OT environments - 24x7x365






.jpeg)