We Give You Continuous Visibility, Rapid Triage, and Decisive Action
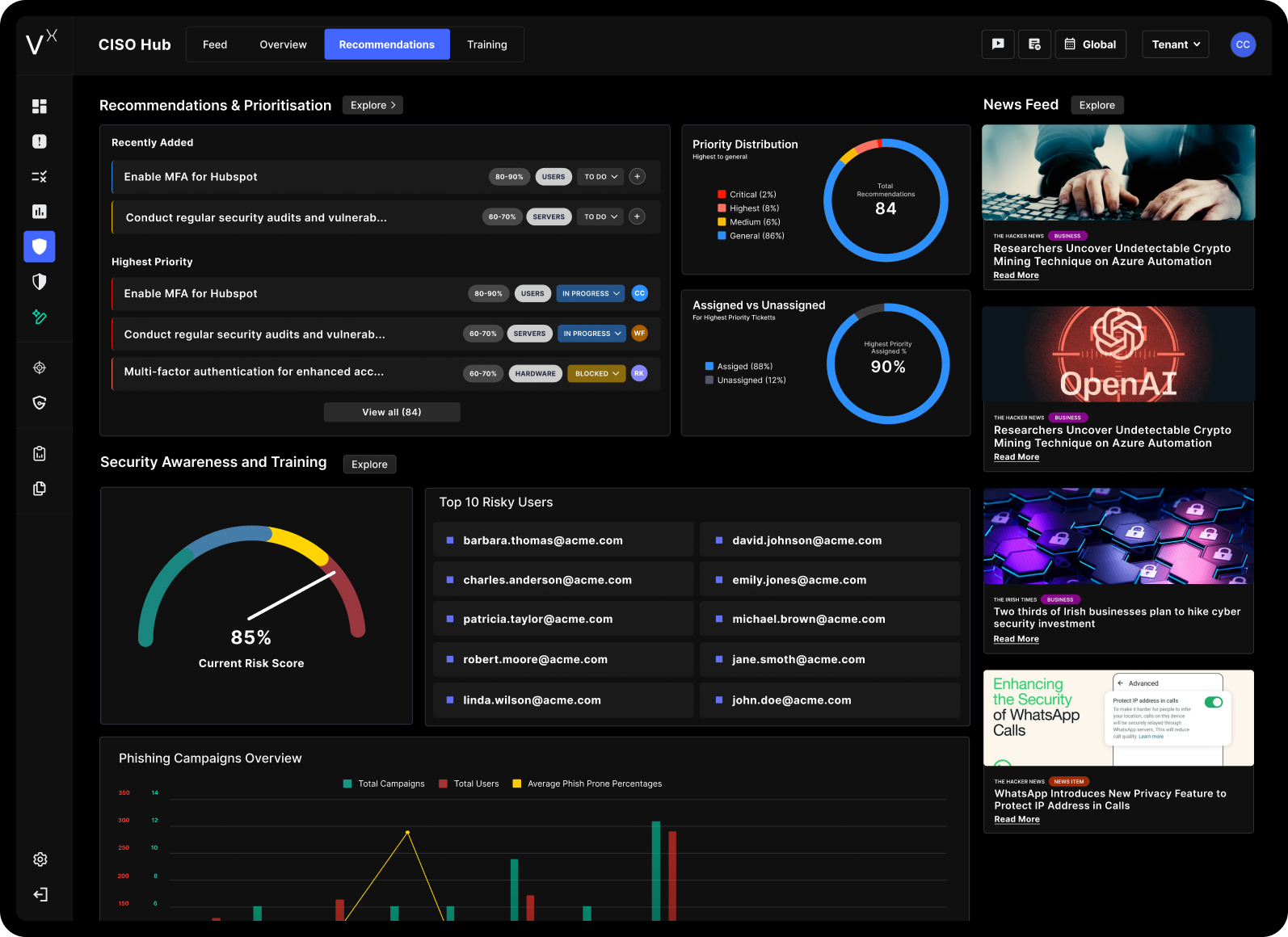
Smarttech247’s 24/7 Security Operations Centre gives you continuous visibility, rapid triage, and decisive action. We combine always-on human expertise with telemetry from your existing tools and our VisionX platform.



.png)






.jpeg)






.png)



