Tuesday, June 8th, 2021
Excel Malware – Cybercriminals are abusing it to distribute

Threat actors are increasingly adopting Excel malware as an initial stage vector to distribute malware such as ZLoader and Quakbot.
A macro is a series of commands that you can use to automate a repeated task, and can be run when you have to perform the task. However, there are risks involved when you work with macros, and you should never enable macros in an Office file unless you’re sure what they do. Unexpected macros can pose a significant security risk to your devices.
Excel Macros
Excel has a macro facility, known as Excel 4 macros (XLM for short) that was the primary macro language prior to the introduction of VBA in Excel 5.0. Most people have long since migrated their Excel 4 macros to VBA; however, some Excel 4 macro capabilities were missing from VBA, which made this migration difficult. Although Microsoft Excel still supports Excel 4.0 (XLM) macros, Microsoft encourages you to migrate them to the latest version of Microsoft Visual Basic for Applications (VBA).
VBA
Beyond the power of scripting VBA to accelerate every-day tasks, you can use VBA to add new functionality to Office applications or to prompt and interact with the user of your documents in ways that are specific to your business needs.
Microsoft themselves warn in their support document that enabling all macros can cause “potentially dangerous code” to run.
Macro settings are located in each individual’s Trust Center. However, for professional Microsoft users, IT administrators can change the default settings to prevent anyone from changing settings that may leave the organization open to a breach.
Change VBA macro settings in the Trust Center
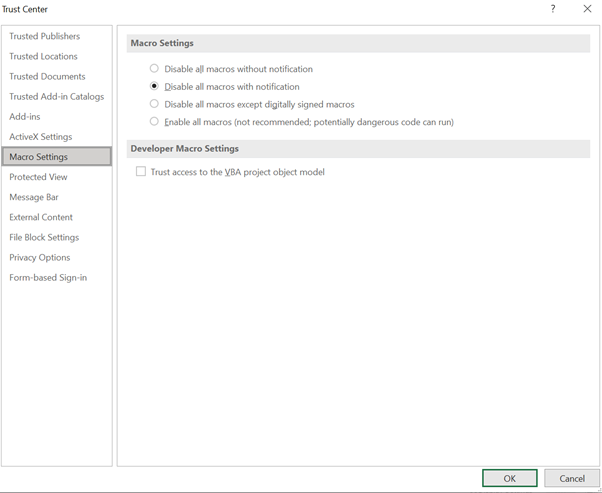
Disable all macros with notification
Macros are disabled, but security alerts appear if there are macros present. Enable macros on a case-by-case basis. In Excel this option is Disable VBA macros with notification and it only applies to VBA macros. This means you can choose to enable macros on a case-by-case basis.
Disable all macros without notification
Macros and security alerts about macros are disabled.
Another setting is “Disable all macros except digitally signed macros.” This displays a security notification for macros that were developed by a certified publisher, allowing you to decide whether to enable or disable them. Any unsigned macros are automatically disabled so you don’t have to deal with them.
Enable all macros (not recommended, potentially dangerous code can run)
All macros run without confirmation. This setting makes your computer vulnerable to potentially malicious code.
Disabling Excel 4.0 Macros
- If you would like to disable only XLM macro settings tenant-wide, without impacting VBA macro settings:
- Uncheck the setting, Enable XLM macros when VBA macros are enabled
- Group Policy Path: User configuration > Administrative templates > Microsoft Excel 2016 > Excel Options > Security > Trust Center
- If you would also like to completely block all XLM macros usage (including in new user created files)
- Enable Group Policy “Prevent Excel from running XLM macros” which is configurable via Group Policy Editor or registry key
- Group Policy Path: User configuration > Administrative templates > Microsoft Excel 2016 > Excel Options > Security > Trust Center
- Registry Key Path: Computer\HKEY_CURRENT_USER\SOFTWARE\Policies\Microsoft\Office\16.0\excel\security
Are you a potential target of an Excel Malware attack?
The below factors may make you more susceptible to an excel malware attack:
- Your device(s) has outdated software i.e. Windows 7
- Browsers and/or operating systems are no longer patched
- No proper backup plan exists
- There is no incident response plan in place
How to protect yourself:
- Monitor your network security 24/7 and be aware of the early indicators of attack
- Stay up-to-date with the latest operating software at all times. Past experience shows (for example, WannaCry 2017) that companies that neglect this area are particularly vulnerable to ransomware attacks.
- Raise employee awareness – a person who knows what to look for will be more effective at countering attacks. Carry out cybersecurity awareness training.
- Prevent attackers from getting access to and disabling your security: choose an advanced solution with a cloud-hosted management console with multi-factor authentication enabled and Role Based Administration to limit access rights.
- Keep regular backups of your most important and current data on an offline storage device. The standard recommendation for backups is to follow the 3-2-1 method: 3 copies of the data, using 2 different systems, 1 of which is offline.
- Have an effective Incident Response plan in place and make sure it is up-to-date.
Please reach out to us for more information: info@smarttech247.com or www.smarttech247.com
Contact Us
The data you supply here will not be added to any mailing list or given to any third party providers without further consent. View our Privacy Policy for more information.