Friday, May 22nd, 2020
CMMC: What it means for defense contractors?

As of June 2020, many companies that work with the US DoD will soon need to meet CMMC requirements to bid on contracts. This has led to many enquiries into what exactly this means for companies and what they should be doing to get compliant.
What’s new?
CMMC will be replacing the existing self-certification model under the Defense Federal Acquisition Regulation Supplement (DFARS) – more specifically NIST 800-171. It is a unified standard for implementing cybersecurity across the defense industrial base, this is estimated to be over 300,000 companies in the supply chain.
So simply, if you currently comply with the existing DFARS and NIST 800-171 requirements you have taken the first step but the new CMMC guidelines establish new expectations and security controls that you must now comply with.
The CMMC is designed to improve protection of controlled unclassified information (CUI) and Covered Defense Information (CDI) within the supply chain.
Previously, contractors were responsible for implementing, monitoring and certifying the security of their information technology systems and any sensitive DoD information stored on or transmitted by those systems. Contractors will remain responsible for implementing critical cybersecurity requirements, but the CMMC now changes this pattern by requiring third-party assessments of contractors’ compliance with certain mandatory capabilities, practices and procedures that can adapt to new and evolving cyber threats from challengers.
CMMC requirements will now be included in sections L and M of DoD requests for information as of June 2020, and in requests for proposals as of Sept. 2020. Organisations need to start identifying their gaps against their target CMMC maturity level to lower their risk of being disqualified when contract bids are released.
What is the process?
The Department of Defense’s CMMC will mean contractors will require a certification process designed to increase visibility and support security into the supply chain. A company’s cyber behaviour based on their controls and practices, will receive a level rating between 1 and 5, which will determine their eligibility to bid on certain contracts.
The five maturity levels range from Level 1 to Level 5 described in the visual below:
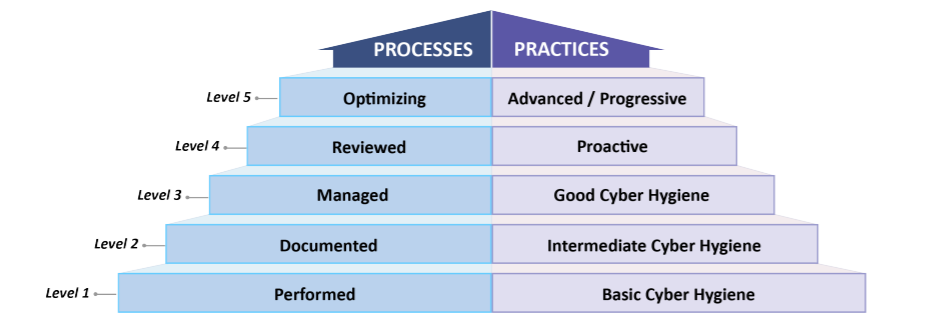
Source: Cybersecurity Maturity Model Certification (CMMC), v. 1, January 30, 2020.
These levels help determine if a contractor’s cybersecurity posture is adequate to handle controlled and classified information.
To be certified at a particular CMMC level, practices and processes must be met within that level as well as the ones below. For example, to meet compliance for level 4, a contractor must also comply with the controls and practices in levels 1,2 and 3.
Are all DoD contractors affected by CMMC?
Every company within the DoD supply chain will be required to get certified to contract with the DoD, not just the defense industrial base. This could affect almost 300,000 contractors and subcontractors.
How will my company become certified?
The CMMC Accreditation Body will accredit CMMC Third Party Assessment Organizations as well as individual assessors. You can get further information and updates on their website.
You can also read more about the new CMMC measures here.
On a final note, while this new CMMC compliance may seem fazing, the main purpose of the CMMC is to improve the way sensitive data is safeguarded and remains secure by ensuring the defense supply chain is protected against security breaches. And if Covid-19 has thought us nothing else, we have to introduce new ways of protecting data because hackers are only getting more creative and ruthless.
To learn more about CMMC as well as more compliance mandates such as EU GDPR, DFARS, TISAX, HIPAA and more join us on May 28th at 4pm for our chat with Getvisibility where you can ask all of your questions on data security and compliance.
Contact Us
The data you supply here will not be added to any mailing list or given to any third party providers without further consent. View our Privacy Policy for more information.
